Computer Health
What Really Happens to Deleted Files on Your Devices?
Do you know what really happens to deleted files on your devices? Learn what goes on after you hit the "delete" button.
Read more

Popular Articles

Security
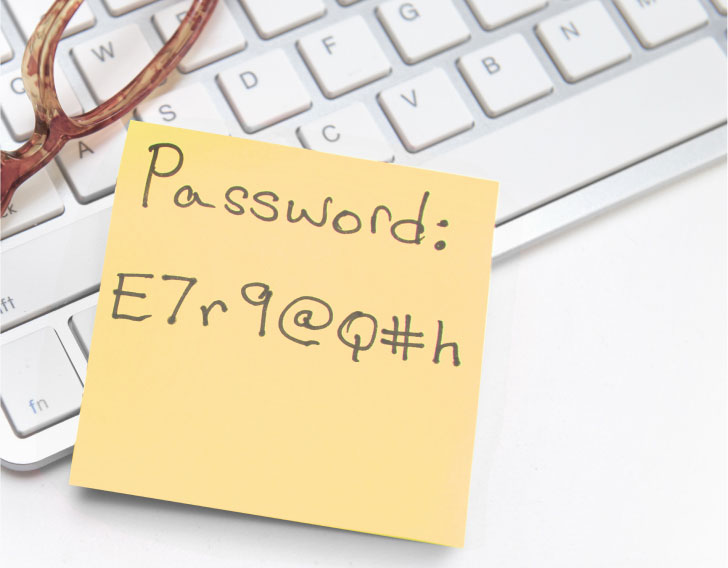
What to Know Before Changing a Password
We all loathe getting the prompt to change a password, but security is important. Learn some tips and best practices before you create your next password. Read more...
Security
The Most Common Password Mistakes (and How to Avoid Them!)
How many passwords do you have? How many do you think could be stronger? Learn the most common mistakes people make with the passwords they create. Read more...

Computer Health
Follow These Steps if You’ve Been Hacked
Do you think you have been hacked? Follow these steps to understand if you have been hacked and what to do if your device has been compromised. Read more...

Sponsored
AOL Desktop Gold
Browse, bank and shop safely with a faster, more secure experience that gives you the familiar look and feel you’ve come to love from AOL. Try it Free*

Security
You're on Vacation – Is Your Personal Data Really Secure?
While you might be on vacation, those that wish to obtain your data never take a break. Get tips to protect your personal data while vacationing. Read more...

Security
Are Your Online Activities Putting You at Risk for Identity Theft?
Do your habits online and offline put you at risk for identity theft? See what you can do or need to stop doing to help reduce the risk of identity theft. Read more...
Top